Cisco Duo CA Expiry: Update Required by March 31
Cisco Duo's CA bundle expires March 31, 2026. Organizations using Duo MFA risk complete authentication lockouts if they don't update their software now.
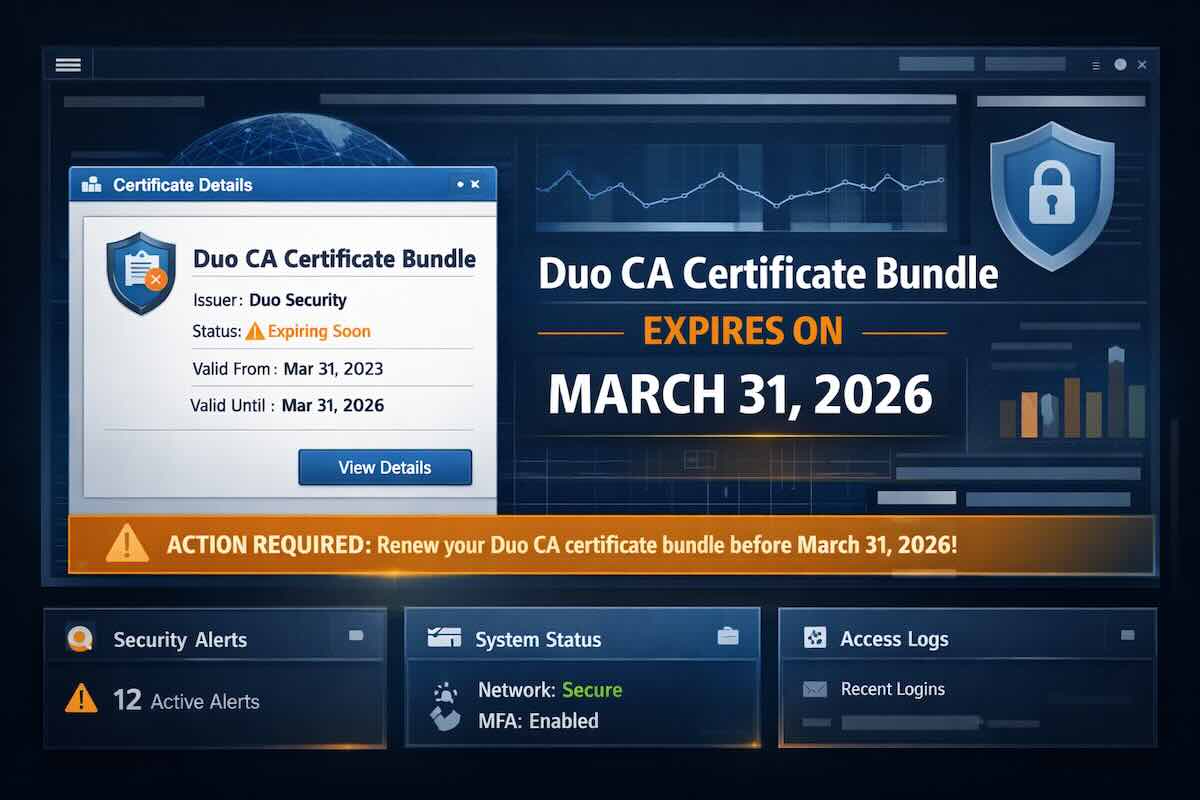
If your organization uses Cisco Duo for multi-factor authentication, you have a two-week window to act before a certificate authority (CA) bundle expiration silently locks users out of your systems. Cisco has issued a formal field notice — FN74372 — warning that unsupported versions of Duo software will stop working on March 31, 2026. This is not a hypothetical future risk. It’s happening in 14 days.
What’s Happening
Duo’s existing CA bundle is expiring as a direct consequence of Mozilla’s ongoing CA distrust policy, which removes older, less trustworthy root certificates from the browser and OS trust stores. The underlying CA certificates that Duo’s software relies on for authenticating connections to Duo’s cloud service are being phased out.
Cisco set a hard operational deadline of March 31, 2026 — ahead of the actual certificate expiry date of April 15, 2026 — to give organizations a buffer to upgrade. After March 31, any Duo integration, mobile app, or Authentication Proxy running on an unsupported version will be unable to complete Duo Push requests or verify authentication. Users will simply be denied access.
The affected products include:
- Duo Mobile — the app used for push-based two-factor authentication
- Authentication Proxy — commonly used for LDAP/RADIUS integrations, SSH logins, and VPN MFA
- Custom API clients — any in-house integration using certificate pinning against Duo’s endpoints
Why This Matters
Cisco Duo is one of the most widely deployed MFA platforms in the world, used across enterprises, universities, healthcare systems, and government agencies. An expired CA bundle doesn’t just mean a browser warning — it means complete authentication failure. When Duo goes down, users can’t log in. VPNs stop working. SSH access breaks. Administrative portals become inaccessible.
The insidious part: this won’t announce itself. There’s no browser pop-up warning the user. Older versions of Duo will simply fail to receive push notifications or complete verification flows, leaving IT teams scrambling to diagnose why logins are suddenly failing across the organization.
This kind of failure mode — silent, widespread, triggered by a certificate expiry upstream — is exactly what makes certificate lifecycle management so difficult to get right.
What You Need to Do
Cisco’s official guidance is clear: update all Duo software to a version that ships with the new CA bundle before March 31, 2026.
- Duo Mobile users: Ensure the app is updated to the latest version on all devices. End users who have auto-updates disabled are especially at risk.
- Authentication Proxy deployments: Review all Authentication Proxy instances and upgrade to a supported version. Cisco’s field notice FN74372 lists compatible versions.
- Custom API clients: If your organization has built custom integrations against the Duo API using certificate pinning, those integrations will need to be updated to trust the new CA chain.
- Inventory your Duo footprint: Many organizations have Duo Authentication Proxy installed in multiple places — perimeter VPNs, internal LDAP servers, remote access gateways. A complete inventory is essential to avoid missing a critical deployment.
Cisco began issuing soft warnings in early February 2026, and authentication degradation (intermittent failures, delayed pushes) has been observable on older versions since then. If you’ve noticed any Duo instability recently, this is likely the cause.
A Broader Lesson About Certificate Infrastructure
This incident is a useful reminder that certificate-related failures don’t only affect your own web properties. Third-party services your organization depends on — MFA providers, CDNs, identity platforms — have their own certificate chains, and when those chains change, your systems can break without warning.
The underlying mechanics are the same as any certificate expiry incident: a CA that was once trusted is no longer, and software that was pinned to that CA stops working. The difference here is that the expiry is happening in a dependency you don’t directly manage, which makes monitoring and advance notice even more critical.
Don’t Get Locked Out
To stay on top of your own certificate expirations and avoid becoming the next headline, consider using SSLcalendar.com to receive timely reminders before your certificates expire — so your team has days to act, not hours. For full visibility into TLS health across your infrastructure, including third-party dependencies, SSLboard.com provides in-depth certificate surveying and vulnerability detection.
The Duo deadline is March 31. Two weeks is enough time — but only if you start now.
Sources: Cisco Field Notice FN74372, Cisco Community: Duo CA bundle update reminder, Sentrium Security: Duo CA bundle update
